How Do WordPress Sites Get Hacked? Here’s What the Data Says
Recently, we wrote about ten security-conscious organisations who use WordPress, ranging from The White House to Facebook, to the Prime Minister of India.
These organisations trust their security to WordPress, but, at the same time, you may have seen news articles referencing WordPress security breaches.
And that leads us to today’s question – if WordPress is secure, how do sites on WordPress get hacked?
Well – spoiler alert – the overarching reasons WordPress sites get hacked are poor user behaviour and implementation. If you have a trusted partner to help you implement WordPress and stay on top of best practices, WordPress as a platform is quite secure, which is why those major organisations put their trust in it.
Let’s not get ahead of ourselves, though – here’s what the data says about how WordPress sites get hacked.
Almost Half of Hacked WordPress Sites are Running Out-Of-Date Software
Let’s start with the biggest correlation between user behaviour and security issues in WordPress:
Out of date software
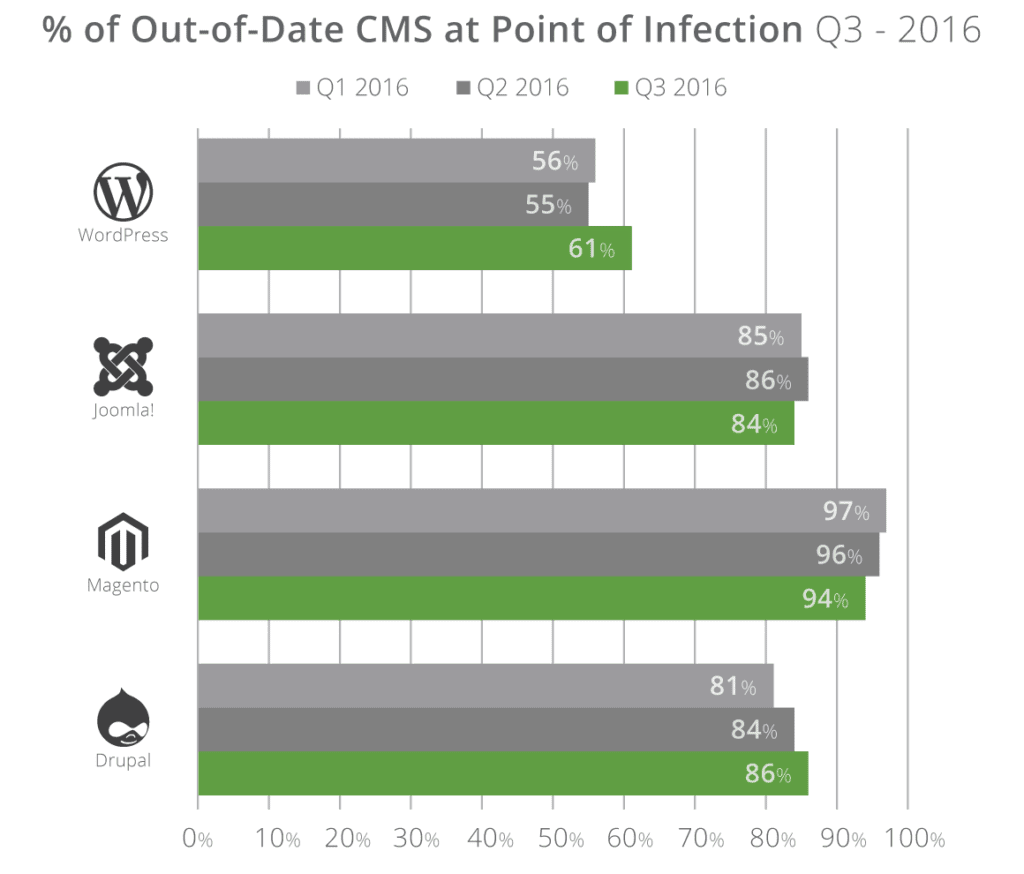
According to Sucuri’s 2018 Hacked Website Trends report, 36.7% of the hacked WordPress sites they analysed were running out-of-date software at the time of infection. That number has been even higher in previous years – typically over 50% and going as high as 61% in Q3 2016.
Here’s why this is important.
WordPress has a dedicated security team as well as a bug bounty program at HackerOne and a huge community of contributors. In the rare situation that a security vulnerability is found, the WordPress team promptly issues a security update. This is true of any platform – security bugs are inevitable. As long as you promptly apply these updates (which are automatically applied by default), your site stays secure.
Unfortunately, though, there’s a segment of webmasters who don’t follow this best practice. Case in point – a 2017 vulnerability in WordPress’ REST API.
Here’s the thing, though – the WordPress team had released a security patch, weeks before the vulnerability was disclosed (WordPress follows a policy of responsible disclosure). All the webmasters who had applied the update were safe and secure.
Think about the Eternal Blue exploit in Windows – Microsoft has long since patched the problem, but it’s still wreaking havoc simply because not everyone has applied the Windows update.
So most of the issues that you’ll see are not a flaw in the current version of WordPress, but rather the exploitation of issues that have already been discovered, patched, and responsibly disclosed. Keep your site updated, and you’ll be safe from most exploits.
Be Careful About Which Plugins You Use
Above, you learned that the WordPress core is secure as long as you keep it updated. But WordPress is a lot more than just the core – it’s also the tens of thousands of plugins that you can use to extend your site.
While the flexibility that plugins afford you is one of the big draws of the WordPress platform, plugins are also one of the biggest vulnerability vectors because there just simply isn’t the same level of attention on their code. The WordPress core has a dedicated security team and millions of eyeballs – the same is not true for plugins.
Plugins can be abandoned, written by inexperienced developers, or sometimes even purchased by malicious actors for nefarious purposes, as was the case in a series of supply chain attacks in 2017.
According to a survey by website owners by Wordfence, of the respondents who knew how their site was hacked, 55.9% of them attributed the issue to their plugins:
Similarly, 25% of all the hacked WordPress sites in Securi’s Q1 2016 report were caused by just three vulnerable plugins. To the previous point, these plugins’ developers had long since patched the issues – but webmasters just hadn’t updated the plugins in question:
With some proactive steps – only using plugins from reputable developers and keeping your plugins updated – you can benefit from WordPress’ plugin flexibility without the drawbacks. We have checklists we run through internally that consider lots of factors before using a plugin.
Lock Down Your Logins
After plugin vulnerabilities, login issues were the next most likely attack vector in Wordfence’s survey. There are a few different issues at play here:
-
- Brute force attack – ~16% of respondents.
- Password theft – ~2% of respondents.
- Phishing – ~2% of respondents.
A malicious actor getting access to your password isn’t a flaw in WordPress itself, but it can still have devastating effects on your site.
Thankfully, WordPress offers a number of solutions to help. Beyond choosing a strong password, WordPress makes it easy to implement other preventive techniques like limiting login attempts, two-factor authentication, and more.
Use Secure Hosting (and Keep Your Hosting Credentials Secure)
Finally, many WordPress sites get hacked not because of WordPress itself, but because malicious actors are able to find a way into the server that houses the WordPress site, either by exploiting poorly configured shared hosting or getting direct access to people’s hosting or FTP accounts.
While these issues have little to do with WordPress itself, you’ll still want to take steps to prevent them:
-
- Choose a secure hosting provider that keeps your account isolated from other accounts on the server. Our preferred hosting partner is WP Engine, which has a lot of built-in technology to keep your site safe.
- Use a strong password, along with two-factor authentication if your host offers that protocol.
- Use SFTP and never store FTP passwords in plain text (which some FTP programs still do).
WordPress is Secure…If You Do It Right
In the end, there’s a reason that big names like Facebook and The White House trust WordPress. Implemented by the right WordPress Agency – WordPress is secure.
Want to make sure you get it right for your site? Reach out to 93digital today and learn how we can use our WordPress expertise to help you create a secure, scalable site that meets your business goals.

10 Security-Conscious Organisations Who Use WordPress

WP Engine Developer Roadmap
Let's Talk
Do you have a web design and build project coming up that you would like to talk about?